OT Vulnerabilies Part 1: Widespread Implications
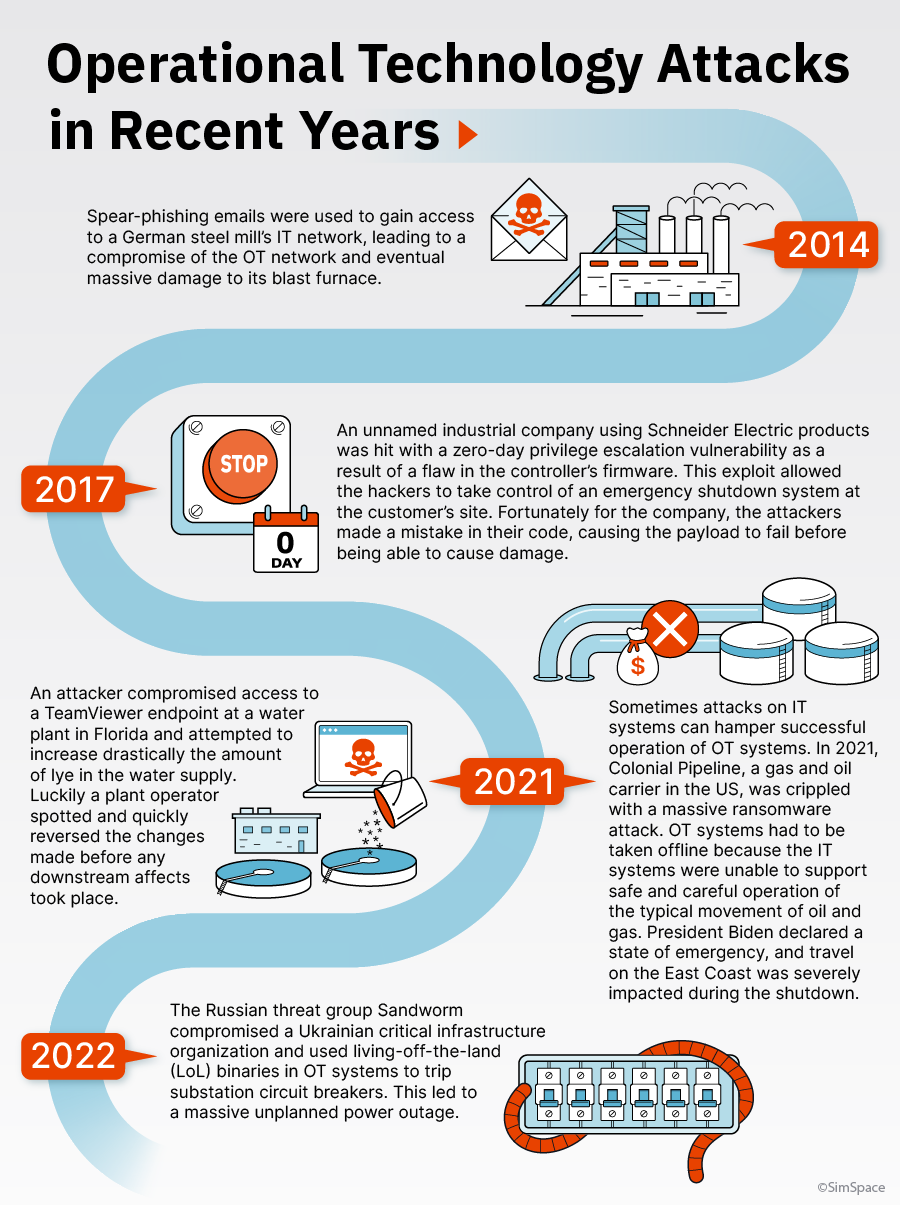
Before we begin, let’s start with a (seemingly) silly question: What do a water treatment facility, a large electric plant, a meat processing plant, and a large brewery have in common? If you happened to muse, “I wonder if these have all been targets of OT infrastructure breaches?”, then you’re right! These operations (and many others like them) may not seem to be ripe targets for global hackers at first glance. However, in this post we aim to pull back the covers just a bit to uncover vulnerabilities inherent in OT systems and the attacks that have been leveraged against them.
Let’s Define Our Terms
![]() Operational Technology (OT) - Simply put, OT is the integration of hardware and software systems that monitor and/or control physical processes in industrial and critical infrastructure settings.
Operational Technology (OT) - Simply put, OT is the integration of hardware and software systems that monitor and/or control physical processes in industrial and critical infrastructure settings.
![]() Programmable Logic Controller (PLC) - PLCs are industrial computers typically used in industrial or manufacturing settings to monitor or control processes. These computers are purpose-built and typically ruggedized with specific form factors to fit into rackmount systems. PLCs are essentially the “atomic elements” of larger systems (discussed next in this list).
Programmable Logic Controller (PLC) - PLCs are industrial computers typically used in industrial or manufacturing settings to monitor or control processes. These computers are purpose-built and typically ruggedized with specific form factors to fit into rackmount systems. PLCs are essentially the “atomic elements” of larger systems (discussed next in this list).
![]() Industrial Control System (ICS) - An ICS exists to monitor or control industrial processes, such as those present in power plants, manufacturing processes, or oil and gas pipelines. Data can be output from the systems for humans to view or fed back into the system to maintain specific parameter states. A distributed control system (DCS) may amalgamate a number of ICSs.
Industrial Control System (ICS) - An ICS exists to monitor or control industrial processes, such as those present in power plants, manufacturing processes, or oil and gas pipelines. Data can be output from the systems for humans to view or fed back into the system to maintain specific parameter states. A distributed control system (DCS) may amalgamate a number of ICSs.
![]() Supervisory Control and Data Acquisition (SCADA) - SCADA systems are typically networks of ICSs that integrate computers and networking equipment for centralized control and monitoring of production data.
Supervisory Control and Data Acquisition (SCADA) - SCADA systems are typically networks of ICSs that integrate computers and networking equipment for centralized control and monitoring of production data.
The Relationship Between IT and OT Security
While IT and OT security share similar characteristics, these two topologies are quite dissimilar in their use case and scope. Fortinet identified four primary differences between the two:
- Operational environment - OT typically operates in industrial environments that may have harsh conditions such as extreme heat, humidity, and/or exposure to dust and debris; IT assets are located in controlled cabinets and facilities. In addition, OT operating systems and programming methods differ extensively from those used in IT.
- Primary objective - OT security is primarily concerned with availability and safety for critical equipment and processes; IT security focuses heavily on data confidentiality, both at rest and in transit.
- Security events - OT systems need to guard against physically destructive events (such as halting a piece of machinery or contaminating a water source). IT systems are more concerned with frequency of attacks due to their vast collection of internet-connected assets.
- Patching frequency - Patching an OT system can be difficult if not nearly impossible in some circumstances depending upon the criticality of a given production process; unpatched vulnerabilities have the potential to linger for longer periods of time. IT systems typically have regular patch cycles - most assets can be scheduled for downtime with minimal disruption to a business.
Conclusion
Critical operations controlled by ICSs and SCADA systems are being targeted by hackers from around the world. These systems may be used to manufacture goods, provide power to citizens, or even control a city’s water supply. In the next post, we take a look at how both governments and commercial operators are bolstering defense capabilities to resist efforts made by nefarious actors.
Thanks so much for reading this post; we look forward to seeing you next time!
Resources Worth Checking Out
If you’re interested in finding out more about securing OT systems, check out the resources below:
- A Brief History of ICS-Tailored Attacks - An informative article by Dark Reading detailing various malware families which have targeted ICSs.
- What is Operational Technology (OT) Cybersecurity? - CyberArk provides a basic synopsis of OT cybersecurity and provides details about current regulations and strategies for this field.
Take the next step toward continuous security improvement
With SimSpace, you can assess
and optimize your complete
security posture — all in one platform
Stay connected
to SimSpace
Want to stay on top of the latest SimSpace
and cybersecurity news and updates?
Please enter your email below
By filling out this form, you agree to SimSpace's terms of use and privacy policy
