
- Posted
- Cybersecurity Models & Frameworks
Cyber Frameworks for the C-Suite
Cyber frameworks are a collection of best practices designed to provide a high-level overview of cybersecurity. Most CISOs use one or a combination of these frameworks to develop their cybersecurity strategies and map testing validation results for driving improvements. NIST Cybersecurity Framework (NIST CFW) and the MITRE ATT&CK Framework are the most common cybersecurity frameworks. The NIST CSF and the MITRE ATT&CK frameworks are essential tools for managing cybersecurity risks, but they differ in scope and focus. As a C-Suite executive, what should you know about the NIST Cybersecurity Framework and the MITRE ATT&CK Framework, and why each matters? Here are some key points C-Suite executives should know about each framework.
NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) was developed by the National Institute of Standards and Technology (NIST) to help organizations manage and reduce their cybersecurity risks. The framework was developed in response to Executive Order 13636, which called for a voluntary framework to improve the cybersecurity and resilience of critical infrastructure in the United States. The NIST CSF consists of guidelines, standards, and best practices that organizations can use to assess and improve their cybersecurity posture. It is designed to be flexible and adaptable so that organizations of all sizes and types can use it to manage their cybersecurity risks in a way that makes sense for their specific needs and circumstances.
- The NIST Cybersecurity Framework is a set of guidelines, standards, and best practices that organizations can use to manage and reduce cybersecurity risks.
- The framework is organized into five functions: Identity, Protect, Detect, Respond, and Recover. These functions represent the critical steps in a cybersecurity risk management designed to help organizations address cybersecurity risks comprehensively and systematically.
- The NIST Cybersecurity Framework is widely used by organizations in both the public and private sectors, and it has become a key reference point for many cybersecurity professionals and policymakers.
- The framework is not a set of regulations but rather a set of guidelines and best practices that organizations can use to manage their cybersecurity risks in a way tailored to their specific needs and circumstances.
- C-Suite executives should understand the NIST Cybersecurity Framework to ensure their organization takes appropriate steps to manage cybersecurity risks and protect against cyber threats.

These functions represent the key steps in a cybersecurity risk management process and are designed to help organizations address cybersecurity risks comprehensively and systematically.
The NIST CSF is widely used by organizations in both the public and private sectors, and it has become a key reference point for many cybersecurity professionals and policymakers. It is not a set of regulations but rather a set of guidelines and best practices that organizations can use to manage their cybersecurity risks in a way that is tailored to their specific needs and circumstances.
MITRE ATT&CK Framework
The MITRE ATT&CK Framework is a knowledge base of adversary tactics, techniques, and procedures (TTPs) based on real-world observations of cyber attacks. The MITRE Corporation developed it is a not-for-profit organization that operates research and development centers sponsored by the U.S. government.
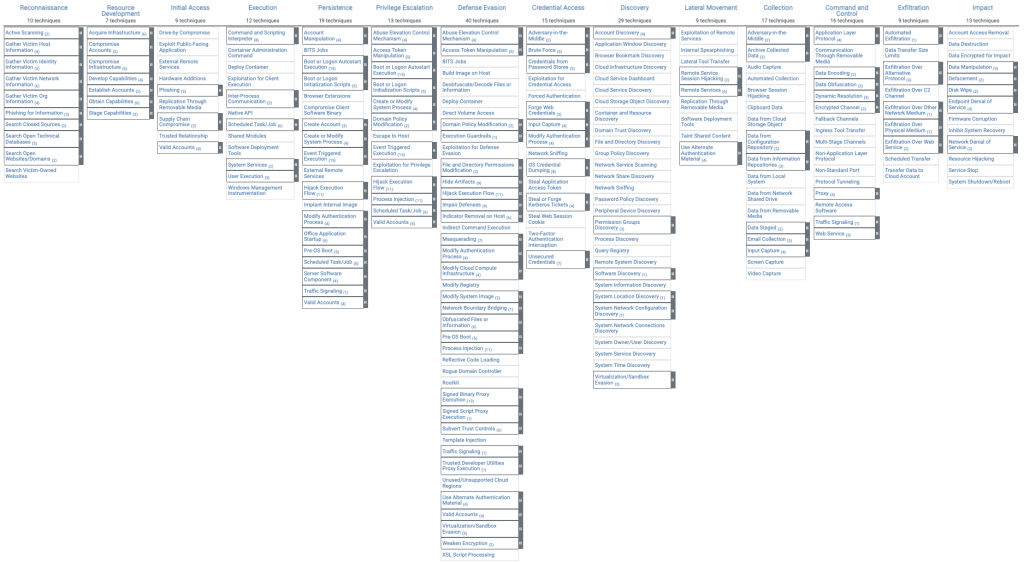
The goal of the MITRE ATT&CK Framework is to provide a common language and methodology for describing and analyzing cyber threats to help organizations better understand and defend against them. It does this by breaking down the entire attack lifecycle into discrete stages and providing a comprehensive list of the TTPs that adversaries use at each stage. This allows organizations to understand the individual tactics that attackers use and how those tactics fit into the broader context of an attack.
- The MITRE ATT&CK Framework is a detailed catalog of adversary tactics, techniques, and procedures (TTPs) based on real-world observations of cyber attacks.
- The goal of the MITRE ATT&CK Framework is to provide a common language and methodology for describing and analyzing cyber threats to help organizations better understand and defend against them.
- The framework is organized into several categories, such as initial access, execution, persistence, and so on, and provides a comprehensive list of the TTPs adversaries use at each stage.
- Cybersecurity professionals widely use the MITRE ATT&CK Framework to understand better the techniques that attackers use and how to defend against them.
- C-Suite executives should understand the MITRE ATT&CK Framework to ensure that their organization is aware of the latest cybersecurity threats and is taking appropriate steps to defend against them.
The MITRE ATT&CK Framework is organized into several categories: initial access, execution, persistence, privilege escalation, defense evasion, credential access, discovery, lateral movement, collection, exfiltration, and command and control. For each category, the framework provides a list of TTPs that adversaries use to carry out attacks and information about how those TTPs can be detected and mitigated.
The MITRE ATT&CK Framework is widely used by cybersecurity professionals and organizations to better understand and defend against cyber threats. It is also used by government agencies, such as the U.S. Department of Defense, to inform their cybersecurity strategies and planning.
5 Things C-Suite Executives Need To Know About Cybersecurity Frameworks
The NIST CFW and MITRE ATT&CK are complementary frameworks required to define, operationalize and implement a meaningful cybersecurity strategy. The NIST CFW provides a high-level cyber security operation model. MITRE ATT&CK provides the tactical mapping of cyber security tools, processes, and techniques required to build a world-class cyber operations team. Here are five ways these cybersecurity frameworks work together to build a better cybersecurity program:
- NIST and MITRE are complementary because they address different aspects of cybersecurity risk management. The NIST Cybersecurity Framework provides a holistic approach to managing cybersecurity risks. In contrast, the MITRE ATT&CK Framework provides a more detailed understanding of the tactics, techniques, and procedures that attackers use to carry out cyber attacks.
- The NIST Cybersecurity Framework and the MITRE ATT&CK Frameworks can be used to create a more comprehensive approach to managing cybersecurity risks. For example, an organization might use the NIST Cybersecurity Framework to assess its overall cybersecurity posture and identify areas for improvement and then use the MITRE ATT&CK Framework to drill down into specific techniques that attackers might use and how to defend against them.
- The NIST Cybersecurity Framework and the MITRE ATT&CK Framework both emphasize the importance of continuous monitoring and improvement. The NIST Cybersecurity Framework recommends that organizations regularly assess their cybersecurity risks and adjust their approach as necessary. At the same time, the MITRE ATT&CK Framework provides real-world observations of new and evolving tactics, techniques, and procedures that organizations can use to provide continuous security improvements.
- The NIST Cybersecurity Framework and the MITRE ATT&CK Framework are both widely recognized and respected in the cybersecurity industry. As a result, organizations that adopt these frameworks can benefit from a common language and methodology for describing and analyzing cyber threats.
- The NIST Cybersecurity Framework and the MITRE ATT&CK Framework both reflect a risk-based approach to cybersecurity. Organizations can prioritize their cybersecurity efforts and allocate resources more effectively by focusing on the most significant threats and vulnerabilities.
Cyber Ranges for NIST CSF and MITRE ATT&CK
At the heart of these frameworks is the need to test and validate your people, processes, and technology. Obviously, CISOs and other C-Suite executives do not want to run testing for attacks and breaches that can compromise production environments. This is why the US Cyber Command, leading financial companies, and thousands of other organizations deploying a cyber range can help support the NIST Cybersecurity Framework and the MITRE ATT&CK Framework in several ways.
- A cyber range is a virtual environment that simulates real-world network and system configurations. It can be used to test and evaluate different cybersecurity strategies and technologies in a safe and controlled environment.
- Organizations can develop and test different approaches to managing cybersecurity risks using a cyber range, including those outlined in the NIST Cybersecurity Framework and the MITRE ATT&CK Framework.
- This allows organizations to identify and address vulnerabilities and gaps in their cybersecurity defenses before exposure to a real-world attack.
- A cyber range can also be used to train cybersecurity professionals on the latest techniques and tools for defending against cyber threats, which can help organizations stay up-to-date on the latest cybersecurity trends and best practices.
- Overall, deploying a cyber range can help organizations better implement and integrate the guidance provided by the NIST Cybersecurity Framework and the MITRE ATT&CK Framework and improve their overall cybersecurity posture.
As C-suite executives are asked hard and demanding questions from their boards, auditors, insurers, customers, and supply-chain partners using cyber ranges to test and validate your cyber security strategy against the NIST CSF and MITRE ATT&CK frameworks with provide your company with analytics required to make informed decisions, balance cyber spending vs. business risks and provide the evidence-based reporting to prove your team is a prudent and effective cybersecurity partner.
Allied governments, militaries, commercial enterprises, and research universities worldwide trust SimSpace as the AI Proving Grounds where human operators and AI agents train and test together in a realistic replica of their production environments to outperform and outsmart any adversary in any terrain. To learn more, visit: http://www.SimSpace.com.